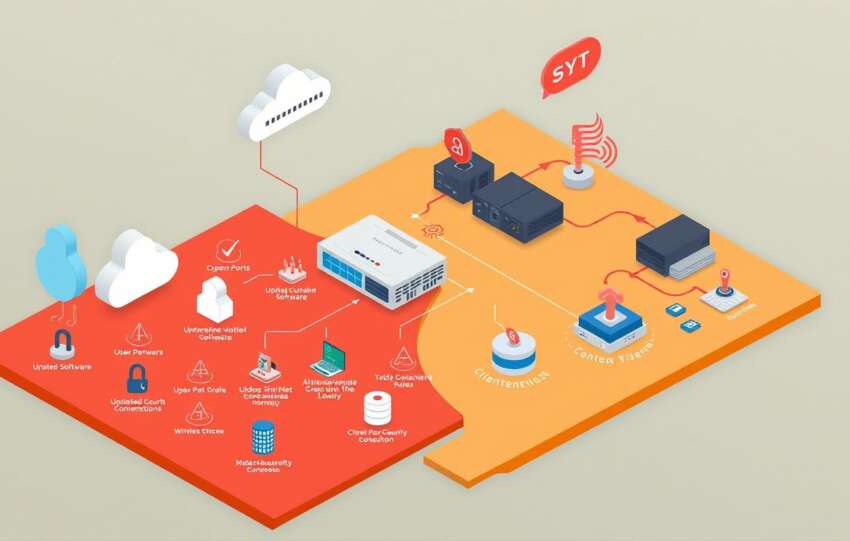
In today's digital world, strong cybersecurity is more important than ever. As we rely more on digital tools, protecting ourselves from cyber threats becomes a top priority. Network vulnerabilities can harm our data and disrupt our work. By knowing and fixing these weaknesses, we can make our online world safer. This article will explore the…